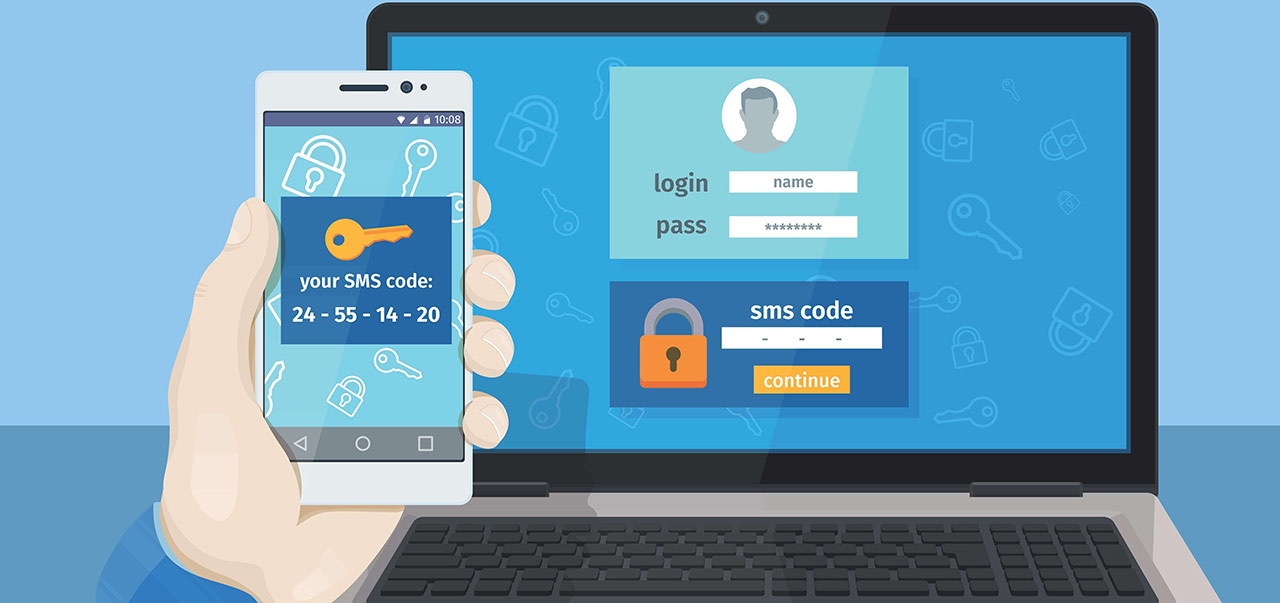
The internet is a dangerous place, replete with shady people looking to steal your personal information. Two-factor authentication or 2FA, has long been considered an important measuare for protecting your online accounts against such activity.
2FA authentication codes are typically sent via text message or via authentication apps. It’s like the bank asking for two forms of ID.
But is two-factor authentication still as secure as everyone originally thought? As usual, hackers and cybercriminals will always find a way to circumvent it.
Piotr Duszynski, a researcher specialist on network security born in Poland, recently announced the launching of a penetration testing tool called “Modlishka”
Modlishka, coming from the Polish word “mantis,” can reportedly bypass login operations for accounts protected by 2FA and enable an attacker to have full control of “cross” origin TLS traffic flow from the victims browsers. It employs a reverse proxy with slight modifications to facilitate phishing attacks.
Not only does Modlishka bypass 2FA, it also saves user credentials in its backend panel to be accessed at a later time by the attacker. It operates between the user and the email provider of the user’s choice, such as Gmail, Outlook or Yahoo, mentions Duszynski. The victim then connects to the Modlishka server, which generates requests to the websites to be spoofed, so the victim won’t be able to found differences between the real site and the spoofed one.
When the copy of the site is created, the victims interact with authentic content of the website; however, al user activity will be logged on the Modlishka server.
Once the site has been supplanted, the victim will interact with authentic content from the legitimate website. The victim can buy online, however, any interaction the victim enters, will be logged on the Modlishka server; this could lead to some variant of identity fraud and other malicious activities.
Is 2FA still safe to use?
Duszynski has said that “2FA isn’t broken. At the end it is all about ‘social engineering’ that you will have to be stay alert about. Which can be e-mail, phone, post or face to face”.
2FA is still leaps and bounds better than no 2FA at all. For now, far too many people are not using any 2FA at all. Thus from an opportunistic attacker perspective, having the much derided 2FA via SMS means you’re a harder target than the user next to you.