A hacking campaign linked to Iran appears to be targeting dozens of domains across the globe by way of domain name system (DNS) hijacking, FireEye’s Mandiant Incident Response and Intelligence team have said.
The attacks, targeting several countries to redirect traffic and harvest credentials, have been linked to persons based in Iran. The activity appears to align with Iranian government interests.
The attacks have managed to compromise a large number of domains run by government, telecommunications and internet infrastructure in the Middle East and North Africa, Europe and North America. In so doing, they change DNS records to direct users to malicious but legitimate-looking domains where email credentials are harvested.
The research team added that “while this campaign employs some traditional tactics, it is differentiated from other Iranian activity we have seen by leveraging DNS hijacking at scale. The attacker uses this technique for their initial foothold, which can then be exploited in a variety of ways”.
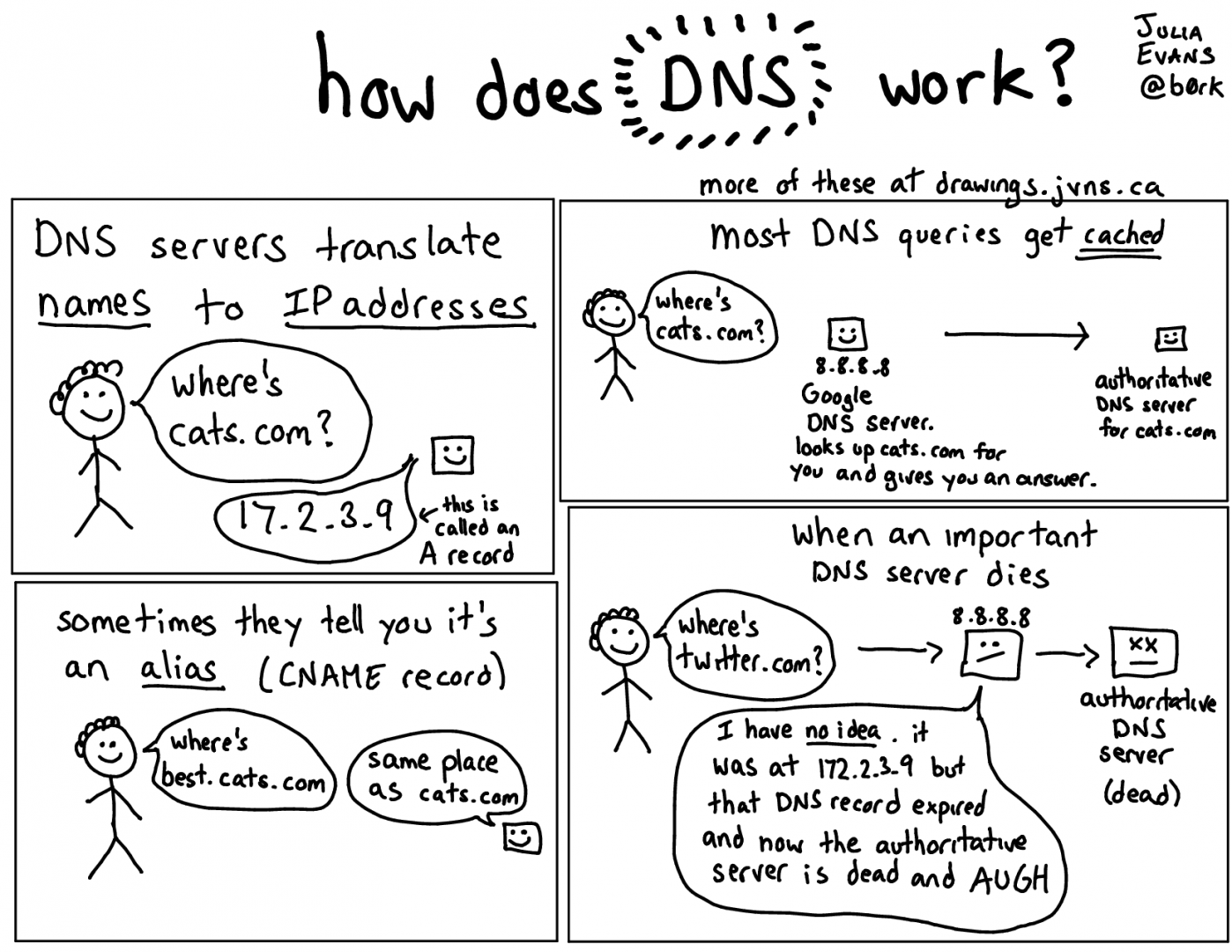
Technique 1, involves the creation of a Let’s Encrypt certificate and a change of the A record (a DNS record that points a logical domain name to the IP address of that domain’s hosting server) to intercept the traffic. This technique was previously documented by Cisco’s TALOS team. The activity described in their blog post is a subset of the activity we have observed.
Technique 2, was a similar method that involves loggin into the admin panel, and from there they hack into the victim’s domain registrar account with a change to the DNS NS records. The NS records specify the servers providing DNS services for that domain name, so in changing them attackers could redirect traffic to a different attacker-controlled server.
Technique 3, uses a DNS redirector, an attacker operations box which responds to DNS requests (as well as altered A and NS records) to redirect victim traffic to attacker-maintained infrastructure.
In all three scenarios the attackers use Let’s Encrypt Certificates. Let’s Encrypt offers a free, automated, and open certificate authority which allows the browsers to establish a connection without any certificate errors as the certificate can be trusted. That helps the attackers slip by without notice as the victim is unaware of any changes and may only notice a slight delay.